Introduction to the Internet of Things
Published on April 07,2017

On your way out of the house, you catch a glow in the corner of your eye. Your umbrella handle is lit up, which means that it has checked the local weather reports (online) and predicts rain. Some will even beep or sing your favourite Maroon 5 song, all with an aim to keep you protected and worriless or you will be rained on (and the interview documents you carried with you will get damaged). You sigh and pick it up. Better still if you dwell in an arid area (making the above example obsolete), you might be having a small irrigated farm to keep your veggies and fruits evergreen. Out of the blue, a sweet voice (like Jarvis’ Morgan Freeman’s) wakes you from your afternoon nap to remind you that your small farm needs to be irrigated. It reminds you of the current humidity levels in the soil plus the current temperature; it has also gone online and retrieved from a big data database, the possible trends in your plants’ performance if you don’t irrigate your farm at the time. These are only a prelude of a very powerful technology; one that has been directly adopted from science fiction. It is the Internet of THINGS (IoT).
For those who understand best through metaphors, we are looking at the idea of enchanted objects, an image which has described technology for millennia but which is especially potent when describing the Internet of Things. The IoT refers to the growing network of internet enabled everyday devices. It refers to scenarios where network connectivity and computing capability extends to objects, sensors (electronic devices that detect physical parameters such as temperature, and generate signals related to the parameter which would be interpreted by a computer to do something such as turn on you cooling fan) and everyday items not normally considered computers, allowing these “smart” devices to generate, exchange and consume data about us and our things with minimal human intervention (or should we say unobtrusively in a seamless way). For the know-alls, no single, universal definition of the IoT exists, so just keep your definition (at least for now).
In the first example, I talked about an umbrella connected to the internet; you can also consider your medicine bottle cap connected to the internet to remind your doctor that you have skipped your medicine. An umbrella and a medicine bottle cap aren’t computers but just things. Things being connected to the internet is something unheard of to many, but IoT brings this scenario to life for everybody lively. But how does it achieve this? Some of you must be familiar with how your computer is able to access a particular resource located on another computer (if you fall in this category, pat yourself on the back). If you don’t, worry not; the explanation follows (study and understand, and pat yourself on the back also). Each computer is assigned a string (combination of characters) of numbers such as 192.168.130.2. This number, known as Internet protocol (IP) address uniquely identifies a device (your computer or phone) on the Internet. Since you cannot master the numbers (some are dynamically assigned hence change over time), the number is resolved to a string of abcd characters such as www.google.com (known as a domain name) that the user can understand and retain in memory. Therefore for each device on the internet, there is an associated IP address. Your device, therefore, knows specifically where the information you want is located. The same is applied in IoT.
Using IP to connect devices other than computers to the Internet is not a new idea. The first Internet “device”—an IP–enabled toaster that could be turned on and off over the Internet—was featured at an Internet conference in 1990. Over the next several years, other “things” were IP–enabled, including a soda, a coffee etc. From these whimsical beginnings, a robust field of research and development into “smart object networking” helped create the foundation for today’s Internet of Things. And now even your TV (only the smart one) is IP enabled hence connected to the internet. Much about the development of the IoT, however, can only be attributed to one of the fascinating trends today; the emergence of low-cost microcontrollers that are sufficiently powerful to connect to the Internet. They are the key to the Internet of Things, where all kinds of devices become the Internet’s interface to the physical world. Because of such inexpensive hardware and easy-to-use development platforms, it is now possible for hobbyists to create systems that interact with the physical world in every conceivable way.
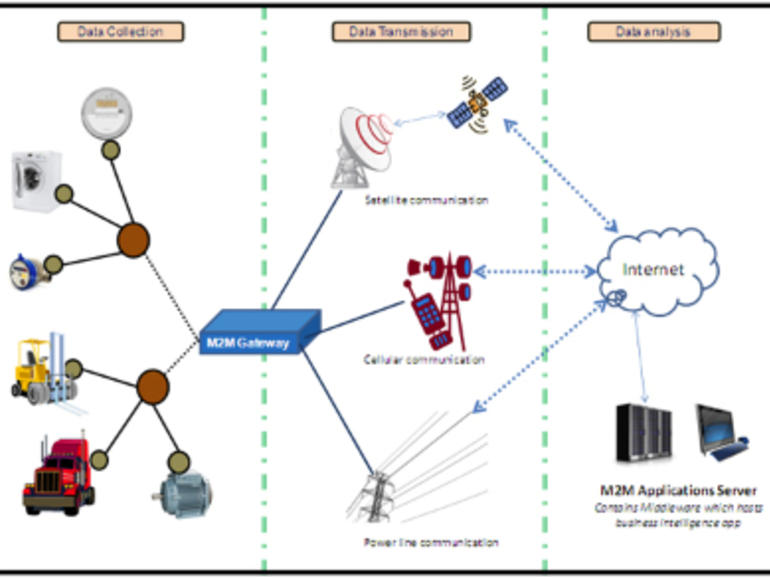
In this paragraph, I will describe briefly the technicals of the IoT i.e. how an IoT system operates. Consider the aforementioned smart irrigation system. The components include a mechatronic system installed in a manual irrigation system. Inside the mechatronic system are a temperature sensor, humidity sensor, a microcontroller (currently the heart of your computer) and an actuator such as a drive mechanism (like a motor). The temperature sensor detects the current temperature of the surrounding; the humidity sensor detects the current soil humidity readings. The two sensors generate signals related to the parameters (temperature and humidity) and relays the signals to the microcontroller (such as PIC16877A microcontroller or Arduino). The signals are processed by the microcontroller which then accesses a specific customized service on the Internet (since it’s powerful). On the Internet, there are specific big data databases for IoT services. Specific platforms for accessing and manipulating data also exists such as the thingworx platform. These platforms and other web related services for the IoT are generally branded the Web of Things. After data manipulation, responses are relayed back to the microcontroller and/or a third party app mostly installed in your handset devices such as a smartphone or a digital watch. The response can initiate a response in the system to open the valve for irrigation and/or remind you of the current situations. Using data analysis (part of the new field of Data Science), you may also get predictions of performance due to an action such as forgetting to irrigate your farm.
The sweet technology above, however, houses very big risks. Consider the statements that follow which were a major concern to the European Union
Lack of Control: Data subjects may lose all control of the dissemination of their data and in practice find themselves under third-party monitoring.
Repurposing of Original Processing: Apparently insignificant data originally collected through a device can be used to infer other information. Therefore, while the user was comfortable with sharing the original information for one specific purpose, he/she may not want to share this secondary information that could be used for totally different purposes.
Intrusive Bringing out of Behaviour Patterns and Profiling: A sufficient amount of data collected and analyzed can reveal specific aspects of individual’s habits, behaviours, and preferences. Domestics raise specific data protection and privacy challenges as an analysis of usage patterns are likely. For instance, devices containing motion sensors can detect and record when a user is at home and what his/her patterns of movement are. This has serious personal security implications.
Information Security Risk: you should be warned that data losses, infection by malware, unauthorized access to personal data, intrusive use of wearable devices, or unlawful surveillance are some of the many risks that stakeholders in the IoT must address.
Yet when peer into the future, I see your smart irrigation system connected to mine. Your umbrella will be connected to mine and your smart tv will be directly connected to mine. Not through their common control platform but through their own library for learning from each other. And when it reaches a time when the development of these smart things follow a smart protocol, Umbrella X will be heard saying, “ What did Mr. John’s umbrella do to to get his attention when it was kept far away from John. Did he call his smart watch or tv.” The smart thing will be interconnected without caring what one is for and the other is not for. It will be a free world for Hackers for I will need not hustle to get to your computer. I will connect to your irrigation system through mine and then to your smart door and into your computer. Unless these fields go back to their drawing boards. Cryptography (new specialized encryption standards), Computer networks (customized communication protocols for IoT), cybersecurity (new security measures such as firewalls and VPNS) etc. IoT is here to stay and advance with us, mind you it will follow Moore’s law. It is a good thing to have. Tell us what you think by leaving a comment below.